News
Location ReminderWritten on 02.06.26 by Ali Abbasi Hi, This is a reminder that this week's tutorial and lecture will be held at a different location. You were informed about this change last month:
Tutorial: Start: 13:00 c.t. CISPA D1 – Room 0.15 (Event Room) Kaiserstraße 21, 66386 St. Ingbert Lecture: Start: 13:15 c.t. CISPA D1 –… Read more Hi, This is a reminder that this week's tutorial and lecture will be held at a different location. You were informed about this change last month:
Tutorial: Start: 13:00 c.t. CISPA D1 – Room 0.15 (Event Room) Kaiserstraße 21, 66386 St. Ingbert Lecture: Start: 13:15 c.t. CISPA D1 – Room 0.15 (Event Room) Kaiserstraße 21, 66386 St. Ingbert
Cheers, Ali
|
|||
Class cancelled tomorrowWritten on 26.05.26 by Ali Abbasi Hi, Unfortunately, we have to cancel the class tomorrow due to our logistical issues. See you next week, Cheers, Ali
|
|||
Exercise 5 submission deadline extendedWritten on 20.05.26 by Pouya Narimani Hi,
The submission deadline for Exercise Sheet 5 is extended until next Wednesday (27th of May) night.
Pouya |
|||
Change of Tutorial and Course location for 2nd and 3rd of JuneWritten on 07.05.26 by Ali Abbasi Hi, Due to politicians visiting CISPA on June 2nd and 3rd, the CISPA building will be closed to the public. Unfortunately, we have been informed that we need to move the course to another location. To make matters worse, the Computer Science department is also unable to provide a room large enough… Read more Hi, Due to politicians visiting CISPA on June 2nd and 3rd, the CISPA building will be closed to the public. Unfortunately, we have been informed that we need to move the course to another location. To make matters worse, the Computer Science department is also unable to provide a room large enough for all students. As a result, for this specific week, the tutorial and lecture will move from the CISPA C0 building on campus to CISPA's D1 building in St. Ingbert. Additionally, the lecture (but not the tutorial) will start 15 minutes late: at 13:15 c.t. instead of 13:00 c.t. The address and room details are below: Tutorial: Start: 13:00 c.t. CISPA D1 – Room 0.15 (Event Room) Kaiserstraße 21, 66386 St. Ingbert Lecture: Start: 13:15 c.t. CISPA D1 – Room 0.15 (Event Room) Kaiserstraße 21, 66386 St. Ingbert There is a bus running every 30 minutes from the university campus to St. Ingbert. We apologize for the inconvenience; this was entirely outside of our control. Cheers, Ali |
|||
Removing inactive students from CMSWritten on 07.05.26 by Ali Abbasi Hi, Just FYI, starting next week, we will remove students who have not submitted their homework from the course cms, as we assume they are dropping and do not see a realistic path to passing. Cheers, Ali
|
|||
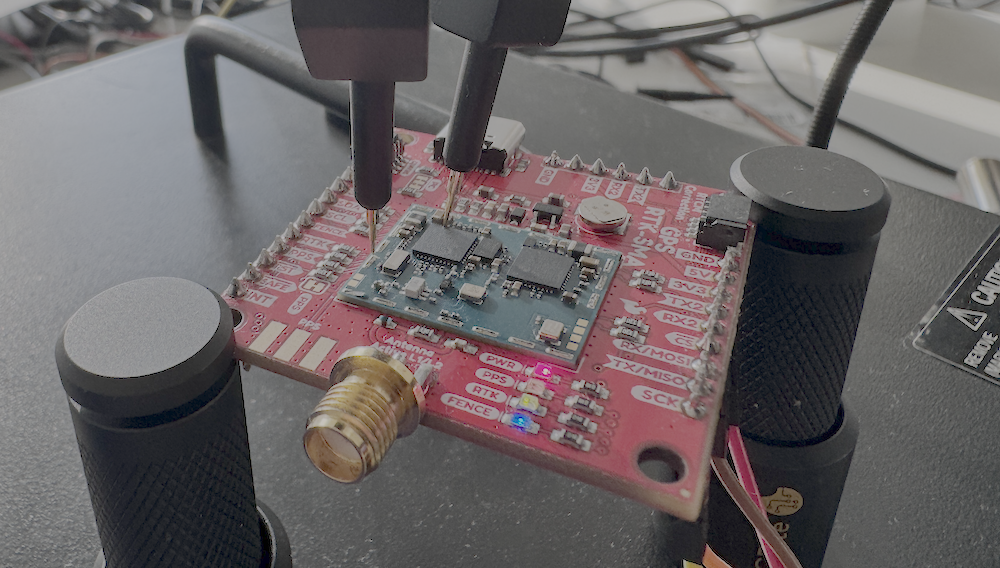
Correction about the day for giving boardsWritten on 04.05.26 by Pouya Narimani Hi,
We will give the boards at Wednesday's lecture.
Best, Pouya |
|||
Board for the next exerciseWritten on 04.05.26 by Pouya Narimani Hi,
For the next exercise (side-channel exercise), you need a board to work with. We will give you the boards in class tomorrow. Please make sure that you attend the class and bring your student ID with you. If you cannot attend tomorrow's lecture, you can pick it up from my office. But… Read more Hi,
For the next exercise (side-channel exercise), you need a board to work with. We will give you the boards in class tomorrow. Please make sure that you attend the class and bring your student ID with you. If you cannot attend tomorrow's lecture, you can pick it up from my office. But before coming to the office, write me an email.
Pouya |
|||
Change of tutorial and lecture location next weekWritten on 30.04.26 by Ali Abbasi Hi, We have been informed by CISPA that we need to change the location of the tutorial and the time of our lecture next week. To this end, this is gonna be the changes:
Hi, We have been informed by CISPA that we need to change the location of the tutorial and the time of our lecture next week. To this end, this is gonna be the changes:
Unfortunately, as you can see, we have to change our location next week, and for the lecture specifically, we even have to change the time, as the university cannot provide a suitable lecture hall at our usual time. As a result, we don't have any option but to move forward with this change.
Cheers, Ali |
|||
Guest Lecture on Reverse EngineeringWritten on 28.04.26 by Ali Abbasi Hi, Just a heads up, tomorrow we have a guest lecture on firmware reverse engineering. The guest of tomorrow generally has training at ReCon/OffensiveCon that usually costs 4k+ Euro and always sells out. Do not miss out! Cheers, Ali
|
|||
Tutorial LocationWritten on 10.04.26 by Ali Abbasi Hi,
Due to Helmholtz's president's visit to CISPA next week, on Tuesday, our tutorial was moved to Room C0-0.05 (basically the lecture hall where we had the lecture).
Ali
|
|||
Tutorial SlotsWritten on 09.04.26 by Julian Rederlechner Hey everyone, we hope you're all settling into the semester well! The first tutorial sessions are coming up, so it’s time to choose your preferred slot. We’ll have three options on Tuesdays:
This schedule will remain the same… Read more Hey everyone, we hope you're all settling into the semester well! The first tutorial sessions are coming up, so it’s time to choose your preferred slot. We’ll have three options on Tuesdays:
This schedule will remain the same for the following dates:
Each slot has limited capacity, so if one works best for your schedule, make sure to sign up early. Registration is open from now until Monday, April 13th at 16:00. Looking forward to seeing you in the tutorials! |
Foundations of Firmware Security

This course introduces students to the security of embedded systems, focusing on identifying and analyzing firmware vulnerabilities. The course begins with core concepts in embedded systems and hardware communication protocols, including UART, SPI, and JTAG. Students will learn to extract and analyze firmware from real-world devices.
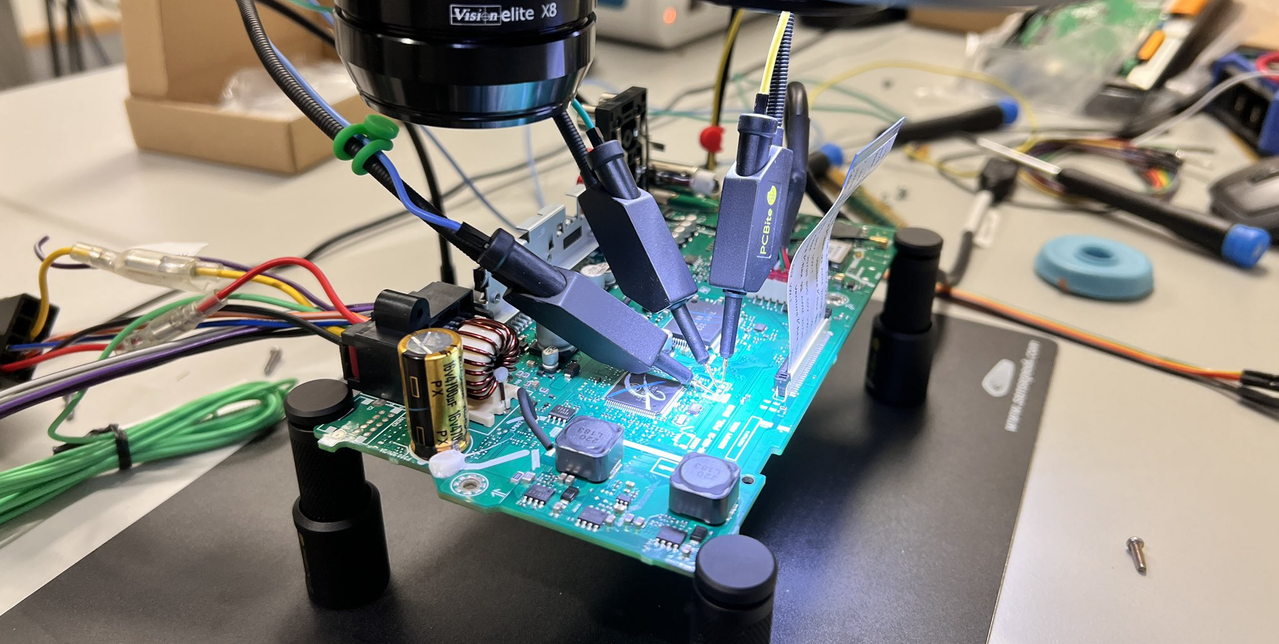
The curriculum then moves into reverse engineering of unknown binaries, teaching foundational techniques for recovering control and data structures. Tools such as Ghidra and QEMU are used for firmware emulation and reverse engineering. Students then explore vulnerability discovery through fuzzing and rehosting techniques, learning to design or adapt fuzzers to analyze embedded firmware. Additional topics include software vulnerabilities, side-channel analysis, and bug triaging. The course also includes a weekly hands-on tutorial session.
Instead of a written exam, students complete a final project report and an oral exam, during which they demonstrate their skills by identifying 0-day vulnerabilities in embedded firmware.
We take pride in the fact that all previous iterations of this course have led students to discover 0-day vulnerabilities in real-world embedded firmware.
Prerequisites
This course is not for the unprepared. You must have hands-on experience in C (and at least a basic understanding of Rust or be willing to learn a bit of Rust), as well as solid knowledge of operating systems and cybersecurity. If you lack these foundations, you will struggle from day one, fall behind, and eventually fail the course.
Most homeworks build on the previous one. If you cannot solve one, you will likely not be able to solve the rest. This requires a serious time investment.
Confidence, Claude Code, "learning ability," or the belief that you are the exception will not save you. Every year, students who are convinced they are different try, and every year, they fail. If you are not prepared, do not enroll.
Course Book:
We recommend the following course books so you can get familiar with the topics:
1. Fuzzing Against the Machine: Automate vulnerability research with emulated IoT devices on QEMU, ISBN: 978-1804614976
2. The Hardware Hacking Handbook: Breaking Embedded Security with Hardware Attacks, ISBN: 978-1593278748
3. Microcontroller Exploits, ISBN: 978-1718503885
More info: https://www.infomath-bib.de/tmp/vorlesungen/info-advanced_foundations-of-firmware-security.html
Time, Location, and Structure
Lectures: CISPA C0 - 0.05 Lecture Hall, Every Wednesday 13:00 to 15:00 (c.t.)
Tutorials: CISPA C0 - 0.01 Presentation Room. The first three tutorials are dependent on the group assignment (3 Groups, Tuesdays 09:00-11:00, 13:00-15:00, and 15:00-17:00), then a weekly tutorial at 09:00-11:00 every Tuesday.
Kickoff Lecture: 8th April 2026,
Kickoff Tutorial: 14th April 2026
Grading
There is no written exam in this course. 40% of your final grades come from tasks and homework. 60% of your grades come from the final project report and your verbal exam. To be admitted to the exam, you must achieve at least 50% of the points from the exercises. The final project is applying the techniques learned in class to a set of targets (bypassing fuzzing obstacles, selecting and building the targets, finding vulnerable code, and writing PoCs). Then the students should write a "Final Project Report". The final project report should contain a step-by-step, detailed description of the whole process. To pass the course, you must score at least 50% on the final oral exam.
Strict no cheating policy
You may discuss the assignments with other students, but you are not allowed to collaborate on the solutions. Your solution should be original and not an existing solution (e.g., from someone else, the internet, LLMs, etc). All submissions will be automatically checked for plagiarism due to our strict no-cheating policy. If we find plagiarism, we will assign 0 points. If you ever get stuck, you can ask questions in the forum or participate in the exercise lessons. We invite you to help fellow students who have asked questions, but avoid giving away the solution. Nobody likes spoilers :)
Regardless, the course is designed in such a way that by cheating, you guarantee your failure on the final project and oral exam.
Verbal Exam
This course does not have a written exam. At the end of the semester, there will be an oral exam of your final project for 30 minutes. All questions of the oral exam are in English. You will need to bring your laptop and present your final project report in a step-by-step manner. We will ask related questions about the report and lectures.
Verbal Exam Date: The verbal exam will take place between July 29th and July 31st. Your specific day depends on your assigned time.
